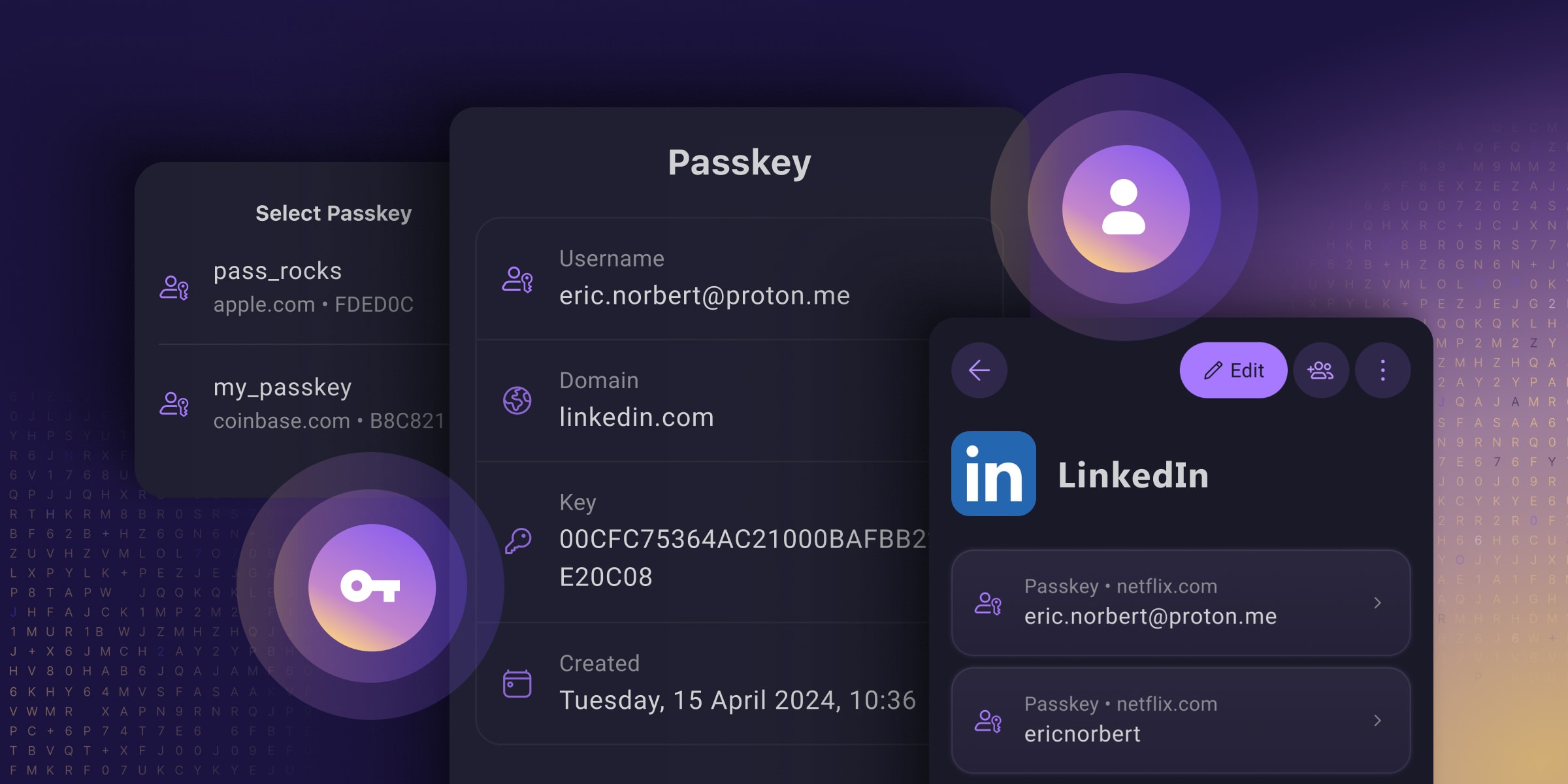
Passkeys are an easy and secure alternative to traditional passwords that can help prevent phishing attacks and make your online experience smoother and safer.
Unfortunately, Big Tech’s rollout of this technology prioritized using passkeys to lock people into their walled gardens over providing universal security for everyone (you have to use their platform, which often does not work across all platforms). And many password managers only support passkeys on specific platforms or provide them with paid plans, meaning you only get to reap passkeys’ security benefits if you can afford them.
They’ve reimagined passkeys, helping them reach their full potential as free, universal, and open-source tech. They have made online privacy and security accessible to everyone, regardless of what device you use or your ability to pay.
I’m still a paying customer of Bitwarden as Proton Pass was up to now still not doing everything, but this may make me re-evaluate using Proton Pass as I’m also a paying customer of Proton Pass. It certainly looks like Proton Pass is advancing at quite a pace, and Proton has already built up a good reputation for private e-mail and an excellent VPN client.
Proton is also the ONLY passkey provider that I’ve seen allowing you to store, share, and export passkeys just like you can with passwords!
See https://proton.me/blog/proton-pass-passkeys
#technology #passkeys #security #ProtonPass #opensource
Proton is also the ONLY passkey provider that I’ve seen allowing you to store, share, and export passkeys just like you can with passwords!
1Password has had this for several months.
As others have mentioned, Bitwarden also has this. This really feels like an ad.
Agreed. Saying PP four times in two sentences triggers my ad sense. Capitalism never capitulates.
I don’t see a way where this isn’t an ad, especially with the end and it’s frustrating.
i looked at it and it literally says passkeys aren’t supported on Android right now. so this is bullshit.
Looks like they are just rolling out support for Android 14 and up.
sry my comment was not clear i meant proton.
Thanks I did not know that. I see they say share via the vault, but don’t specifically mention exporting, as in to a file for importing elsewhere outside 1Password. But certainly LastPass, Bitwarden and others I’d looked at were not exporting the passkeys.
Bitwarden only works on the desktop with a browser extension. So as much as I have Passkeys in Bitwarden they are not usable on my phone :(
Doesn’t Bitwarden already have that feature? https://bitwarden.com/passwordless-passkeys/
Bitwarden currently only supports storing and using Passkeys via the browser extension. You cannot use them on mobile.
Ah I see. Hope to see it brought to mobile soon.
They’re rewriting their mobile apps to make it possible
But the Bitwarden extension works on Android Firefox, so you could probably use it that way.
Seems that way? Although I can’t seem to create a passkey somehow. Or is that how it works? Should I be able to create one on a free Bitwarden plan?
Edit: only on browser extension, got it.
Yes, but as I said, as of yesterday still not implemented on mobile.
I don’t think it has the ability to export/share.
Like in a file?
Bitwarden already syncs between PC and phone.
By “Share”, I assumed with other password managers that supported PassKeys.
It doesn’t necessarily have to be a file, it could be the config like a TOTP code is.
When you say bitwarden syncs between PC and phone, which service does it sync with on these platforms? I didn’t know bitwarden synced with any other service.
Yep, the title is incorrect.reading is hardNo it isn’t. Passkeys cannot be used on mobile Bitwarden, only the browser extension.
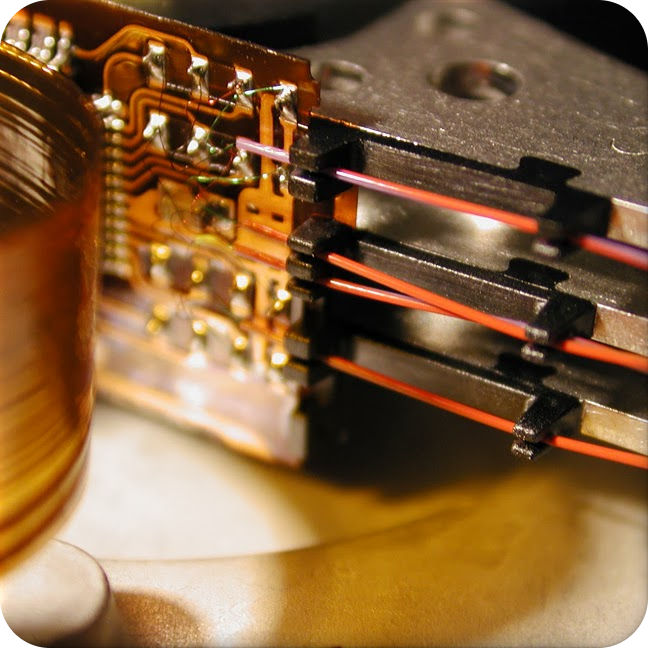
Passkey storage
Note
Saving and using passkeys are a feature of the Bitwarden browser extension. Other Bitwarden clients can be used to view the saved passkey.
https://bitwarden.com/help/storing-passkeys/
I really want to like Proton and all their shit, but they seem to heavily advertise everything they have on every software and product they have in a very intrusive and annoying way.
Simply logging into Proton mail and being bombarded by Proton promotional shit feels like Google all over again.
The app reminds me constantly that I’m a piece of shit for not supporting them by subscribing to their VPN, etc etc.
I would rather they make money from advertising their own pretty awesome services than from advertising unsustainable (environmentally, but also unsustainable for the fucking soul!) bullshit via blood sucking multinational tech companies that prey on the masses with whatever data they can automatically dig up on you. The revenue Proton makes from converting free customers to paid allows them to grow a freely available service that is a user-friendly and is a technical rival of the surveillance capitalists.
My take is:
- If you’re the sort of person that is convinced your requirements need some custom covert ops pagan voodoo self hosted data center in an old cold war era bunker, don’t let me stop you. You crack right on mate and good luck (sounds like you need it!).
- If you want the sorts of services Proton provides, but don’t want to be fucked, then Proton are a good shout.
- If you can afford it, pay for it. It makes the experience smoother and keeps a relatively small but decent company going in an ocean of massive cunts.
- If you can’t afford it and don’t want to use the free version of Proton, I hear Google and Microsoft will happily buy your soul and sell your data.
You’re just going to rub people the wrong way being condescending like that. Find another way to try and bring people to your point of view.
And no, I’m not a shill for Google or Microsoft, I’m a happily paying user of Proton’s products.
People are perfectly within their rights to be rubbed up the wrong way.
Find another way to try and bring people to your point of view
Thanks for your great example of condescension for clarity. A little unsolicited feedback though… other people, unaware of your virtuous intent, might view it as a petty attempt to belittle a stranger on the internet. Other than that, a solid comment. B+
… that’s condescending.
People are perfectly within their rights to be rubbed up the wrong way.
Except in Florida and Texas. That shit gets you arrested these days.
Or so I hear.
You seem nice. _
If you’re the sort of person that is convinced your requirements need some custom covert ops pagan voodoo self hosted data center in an old cold war era bunker, don’t let me stop you. You crack right on mate and good luck
Can you give an actual example of this or are you just making a broad accusation against anyone that uses something other than Proton?
The initial point wasn’t against supporting these services or them making money, it’s the aggressiveness of the advertising. It shows a degree of disrespect for the users when they refuse to leave them alone.
Can you give an actual example of this or are you just making a broad accusation against anyone that uses something other than Proton?
The quote you are referring to is about people who have such specialised security needs that they choose to self-host. i.e. its about people who won’t use Proton because it doesn’t suit their needs. The only ‘accusations’ in the post are against Google & Microsoft, who are accused of buying the souls of their users and selling their data - which I think is a fair accusation. No other company or service is referred to, explicitly or implicitly.
No accusations intended. My point is if you’re clued up enough to be comfortable making your own decisions then fill your boots. I’m not here to convince you. The “aggressive” advertising is the only way they are able generate revenue. And I’m fine with that compared to the alternatives. I find it far more disrespectful to have my data skimmed and monetised by a system of exploitative consumption.
And yet I missed their announcement about their passkeys. In today’s competitive world, I think any company that does not advertise in some way, is really not going to survive (as much as I don’t like ads either). Maybe I don’t see that much as I am paying.
I was getting these advertisements, even as a paid user, just before Christmas. Multiple other people have complained about it both here and on Reddit too. It seems to have gotten better now, but I know a few people have been quite turned off by this.
You can disable it from proton mail settings
Are you talking about the emails?
Yes
I wasn’t 🙃
Oh yeah the UI stuff was a bug, they’ve fixed it already
Do you have emails from them disabled? I got an email about the launch, but yeah, I haven’t seen much mention of it elsewhere.
No just have “Proton for Business newsletter” disabled but I see many of their mails say only once a quarter etc. So seems they don’t send out every month.
This is simply not true. If your products are good your customers will do the marketing for you.
True, and the reverse is also true when a product is bad. I blog usually about what I’m interested in testing out, and when I see if may be worth me moving to a different service.
I haven’t noticed much beyond emails about general product news.
That’s compared to Feedly which actively would popup “hey! have you considered paying us like… 2k/yr (or maybe it was 2k/month) for some service you don’t care about that really should be part of our normal RSS product that you’re already paying like 200/yr for? Also there’s no way to turn these notifications off and we’re going to keep sending them periodically. Oh! And we’re not going to work on anything you might find interesting or reasonably priced, so … have fun!”
You get ads to subscribe to a service while using the free tier? Huh, that’s weird…
When I set up my account, then during setup they asked if I wanted to get email notifications about their products and later it is also available and clearly marked in the account settings. I’d assume that if I turned those setting off, I’d stop getting those emails.
That being said, I have gotten 8 notifications from them over the last 3 months. I have all newsletters and promotional content enabled. This isn’t much imo
I have both paid and accounts with Proton and I have no idea what you’re talking about.
Yes, they make it clear they offer suite of services, and notify you of new services being launched, but my screen isn’t saturated, and my workflow isn’t negatively impacted.
…and they are nothing like Google in terms of self promotion, to say nothing of Google’s business practices.
you’re able to unsubscribe from all those protomtions . . . that is in settings. Personally, a once-a-month newsletter of everything that is new is helpful bc I don’t need to put in the effort tlinto keeping up
deleted by creator
Is this an ad?
No, an ad would have come out when it was launched, and an ad would try to sell something?
an ad would try to sell something?
You’re trying to sell people on Proton over Bitwarden.
Firstly, the point was made that the passkey functionality in Proton Pass is free (no account needed or “selling”) and that is for unlimited logins. Anyone can just use it. I pay for, and am still using Bitwarden. I posted about this because it is interesting that Pass has implemented passkeys for mobile, while I still wait for Bitwarden, so I’m interested in testing this out with Proton Pass. I post about all sorts of things that I find interesting, and sometimes I do switch my services across if I find it can match or better what I already use. That’s the bottom line.
I was just as interested when I was considering moving from LastPass to Bitwarden, but then I was accused of “selling” free Bitwarden to people. Everyone must make up their own minds as their circumstances are different. But if no-one posted about what they found interesting, we’d have no Lemmy, and we’d all forever just stay stuck on whatever we personally know. Certainly Bitwarden and Proton Pass are not the only good password managers out there, but this week I was interested to see an article about Proton Pass, and I had not even known they’d rolled out passkeys yet. It seems like quite a few others did not either.
I’m sure others also post about what new stuff 1Password has just rolled out, and I’d be interested to hear about that too. That is how I decide whether I want to try something better.
If I wanted to try to sell something, I’m sure Proton Pass probably has some loyalty link for paid accounts, but no, you did not see me sharing anything like that. I mentioned the access was free.
This reads achingly like an advert pretenting to be a social media post. BitWarden works fine for third party pass keys on every site I’ve used it on, ta - and I can self-host it.
But you seem to have missed the heading of the post? Bitwarden still (after many months) has not rolled out passkeys to mobile devices. That was actually the point of the post, and Bitwarden needs to start innovating a bit faster as others are overtaking in regard to passkeys. So, you can’t be using Bitwarden for your passkey logins on mobile?
Bitwarden only have not done it because their Android and IOS apps are using xamarin which prevents this implementation at it’s current version, so they have to rewrite app first. It’s not a matter “they have to start innovating”. It’s a technical problem that takes time to solve.
Ah thanks for explaining that. It just makes it then difficult to fully move to passkeys with Bitwarden, which is why I’ve been waiting so long, and why I never stayed using Google or Apple’s passkeys.
Why are you trying to frame this as a race? The vast majority of users don’t care about passkeys yet.
The point of the post is completely irrelevant because Bitwarden already announced they’re implementing this in the next release of the app already.
It’s not a race and I would not even start to use passkeys until I know they can move with me across devices and OSs. Also, most sites that do offer passkeys, still offer highly insecure password resets which really undermines the security that passkeys should offer. I waited a long time for Bitwarden to start with passkeys, and they were going to be the answer to fully portable passkeys (I’ve been waiting so that I know my passkeys will work across all my devices and OSs). Now I’m waiting for mobile implementation before I can get going. I do hope they will also be offering exporting of passkeys, like you can currently export your passwords to other services.
I hear Bitwarden is redoing its mobile app, so maybe with that redesign will come some passkey support. 🤷♂️🤞
all devices
Lies, there’s no Linux app yet. As usual, Proton Inc continues to treat Linux users as third-class citizens, all whilst claiming they care about privacy and security.
Edit: They don’t even have a macOS app yet lol.

I tried their mail app, it’s Electron garbage. I love all their other stuff tho.
TBH KeepassXC + SyncThing is superior in every way.
I’m using the browser add-on in Linux across all my browsers. I do have the Bitwarden app for Linux, but to be honest I never open it as it is a pain to have to open a separate app, and then copy and paste. Isn’t it just more seamless to let it replace the browser password manager on Linux? If I want to tidy up my Bitwarden vault, I also do that in the browser.
Passwords are used in more places than just browsers though. If there wasn’t any need for a dedicated app, why did they bother making one for Windows?
But personally, I dislike Bitwarden as well. I prefer KeepassXC instead, as it works fully offline and I don’t need to depend on a cloud-based provider (or spin up a server). The best part about KeepassXC is that it supports auto-typing credentials, so you don’t need to copy-paste - and it works across a multitude of apps, such as remote desktop / terminal sessions.
I have the app and the browser extension. I usually open the extension and copy from there rather than use the app for things outside of the browser. It’s just quicker.
This is what I do as well. I always have Firefox running and can easily search the extension for whatever password I need and it is just as easy to copy from there as opening another tool.
That being said the iOS app is great for when I am away from my laptop.
deleted by creator
Have you used KeepassXC or BitWarden? Just curious.
deleted by creator
Ah, nice! Yeah, I have a seperate KeepassXC on my work Mac, so the ones on my Linux desktop never touch. I do sync my general Obsidian notebook back and forth which is nice. Client specific notes stay seperate due to NDA’s. It’s easier having to seperate devices with a KVM.
Vaultwarden is completely in my hands though
True, just hope they eventually get passkeys for mobile.
If you’re on Android, you could probably use the Firefox extension.
Just like the Bitwarden app on Android, the Proton Pass one sits in the background to help with auto-fill on any browser form, irrespective of which browser it is.
They will have to rip Bitwarden (soon Vaultwarden) from my cold dead hands.
When are they changing their name? I didn’t even know
They aren’t. Vaultwarden is the selfhosted version.
True, it is good, but they need to speed up on passkeys for mobile as many do use mobile devices and what’s the point of having passkeys on desktop.
I have a question that is kind of off topic. If I use a password manager and generally use randomized secure passwords, do passkeys offer any additional security?
By practicing good password behavior, I have struggled to see how the benefits of passkeys out weigh the hassles.
Yes, passkeys are not brute-forcible, and are phishing resistant.
Whether or not they provide more security depends on how fully they’re implemented. A service that’s fully implemented them, like PlayStation for example, will remove the password from your account after activating your passkey.
Some websites have half-assed their implementations where you can use a passkey or a password to log in. In that scenario, your account isn’t really any more secure, it’s just a more convenient way to log in.
Are sufficiently long passwords susceptible to brute force attacks?
Don’t passkeys get that feature by just being longer?
Are sufficiently long passwords susceptible to brute force attacks?
Yes. Thought obviously the odds of success go down the longer and more complex that password.
Don’t passkeys get that feature by just being longer?
Put simply… no. Passkeys aren’t just ”longer passwords” sent to the same place. Unlike passwords, Passkeys aren’t a “shared secret” that you’re sending to the service you’re authenticating to. Passkeys use asymmetric encryption and are neither sent to nor stored on the server you’re authenticating to. Your passkey is a private key stored on your device and secured by biometrics, the paired public key for which lives on the server you created the passkey to authenticate to.
In a traditional brute force operation, you’re sending guesses to a server that knows your password. If you send the correct guess, you get in. It’s also possible to steal the password from the server and brute force that offline.
With a passkey on the other hand, the server uses your public key to encrypt a string in a challenge message, this string can only be decrypted by your passkey. You then send a response that’s encrypted by your private key, which can then only be decrypted by the public key on the server. So the thing you’re sending to the server to authenticate isn’t your passkey, and it’s unique every time you log in.
So could you perform some kind of operation that would technically still be a kind of brute force? Theoretically yeah. But even so you’d be limited to brute forcing against the server, which isn’t very effective even against passwords. However you would not at all be susceptible to offline brute forcing based on the capture of a passkey either in flight by breaking encryption, or by breaching the server, because your passkey never leaves your device.
Thank you, that was a really helpful explanation that I haven’t seen elsewhere. It helps a lot and I think I now understand the difference between passwords and passkeys.
I still don’t like the hassle inherent in passkeys, but at least I understand it now.
Oh yeah no problem. The internet is flooded with high level answers that don’t really explain it in any detail.
I wonder what hassle you’re having? Passkeys should be much less hassle than passwords.
The hassle is that I have to have a second device to login with, and I have to keep that device with me and functioning at all times.
Obvious answer is of course my phone, but I’ve had a few situations where I needed to access an account on a new system and didn’t have a 2nd device available.
Unless you lose it or have it stolen.
Passkeys can’t be lost or stolen in the same way passwords can. They aren’t something you need to learn and are at risk of forgetting, and unlike passwords they never leave your device so they can’t be intercepted, or stolen in a server side data breach. In order for a passkey to be stolen, somebody would need to both steal your phone, and force you at gunpoint to unlock access to the passkey using biometrics.
So they’re much, much harder to lose or “steal”, and the only way they can be stolen, could similarly be used against you to steal your password.
Yes, I think this person is precisely and exactly asking, what if someone steals your phone?
Not so much that they will get access to your data. Even though on secops it’s a given that access to the device is game over. Even if the device is fully encrypted, it’s just a matter of time (even if that time is infinite) to get access.
But, now the user is locked out of their digital life. How do you get back in? There’s nothing you can use to authenticate yourself in with the server if all you had was a passkey. Your data is now inaccessible, great, but utterly lost, not so great. One workaround is to have more than one device with access to all your accounts and never have them in the same physical space or travel with them at the same time. So you don’t lose them both. Or, how most implementers are doing, using all security systems simultaneously. Passkey, passwords, TOTP, 2FA, all at the same time. Such that you can go back into your account if all your devices are compromised.
But, now the user is locked out of their digital life. How do you get back in? There’s nothing you can use to authenticate yourself in with the server if all you had was a passkey.
I’m still not sure what the question is. The same way you would with a password. Using an authenticator app also ties authentication to a single device and yet you don’t seem worried about that. Using “all security systems simultaneously” is not a solution to this problem you’ve suggested which I don’t think really exists. By using all security systems you’re just making your service less secure, not more.
I’m still not sure what the question is.
Using an authenticator app also ties authentication to a single device and yet you don’t seem worried about that.
I didn’t mention it because the comment is not about that (?). But it does worry me. This is why I have 2FA with my authentication/password manager, and do make sure to remember my password to that, because it is the one service remembering all my passwords, TOPTs and passkeys.
By using all security systems you’re just making your service less secure
I agree that it is less secure, but it’s a necessary evil. Furthermore, it’s mandatory. Security and convenience are always at odds. Passkeys theoretically hit a sweet spot of both qualities. But they come with a higher potential for a possible theoretical lockout.
Let’s assume you have an email, you access this via a passkey authenticator that remembers all your passkeys. To access the authenticator you have to provide either a fingerprint on your phone or a password + OTP to your email. This is a system on potential lockout.
If your phone is stolen or destroyed, now you can’t use the phone to access your email, nor login into your email to verify your access to the passkey authenticator. Now you are locked out of your entire digital life. This is not a rare occurrence, it happens everyday. The only reason it’s not catastrophic is because some part of the chain is password only, and the person remembers the password. Or the second factor is on a trusted third party (like cellular carriers reinstating phone numbers via ID check).
Just like welding all doors and windows shut, yes it is more secure, but you also locked yourself out of the house. You want to still be able to enter the house.
Passkeys theoretically hit a sweet spot of both qualities. But they come with a higher potential for a possible theoretical lockout.
But they don’t. I think this is where your confusion is. I think you’re worrying over a problem that doesn’t exist.
Now you are locked out of your entire digital life. This is not a rare occurrence, it happens everyday.
It does not.
If you’re scared of losing both your device and your recovery codes for TOTP, to the point that you store those in your password manager, and you’re happy with that solution, then just store your passkeys in your password manager. Thats literally what this post is about.
And even if you store your passkeys on device for an iPhone for example, they’re stored in your iCloud Keychain which can be recovered if you lose your device. Theres also just nothing about Passkeys that prevent a service from offering an account recovery service.
If you’re already using 2FA, then Passkeys do not pose any additional risk to being “locked out” of your accounts. They actually have less risk usually.
deleted by creator
Yes, passkeys are public private keys, so a site only ever sees your public key. Your device does the match with the private key. So in that way, no-one can hack the service site and steal your password. But your private key on your device has to stay very private, and should be synced to another device, because if you lose your private key then essentially you can’t login in. If a site offers a backup “password reset via e-mail” then they have rubbish security anyway.
Everyone should downvote ads type post if you want to keep the community clean.
Can I get an explanation on what exactly passkeys are? I already use bitwarden for passwords, is there any good reason to switch to passkeys if that works for me?
Passkeys are a form of passwordless authentication. You store them in Bitwarden like regular passwords, but when you want to access a site that supports them (e.g. eBay) instead of asking for you password and autofilling or copy pasting it from Bitwarden your Bitwarden pops up and asks you if you want to login and it just happens (if you have multiple passkeys associated with a site you can select which you want to use). That’s it. No password fields which get autofilled and no password in your clipboard (history).
Sounds a lot like SSO no?
It is a similar experience, but you don’t need any infrastructure for it. Everything is handled by your device.
Thanks for the explanation. From the sound of it I’ll probably stick with passwords—i like being able to copy them, cause I’m often signing in to an application, not a website, etc.
That’s a reasonable decision. While passkeys are usually considered much safer than passwords they are not really common. It is mostly the big services (Google, Microsoft, eBay) which have implemented them. Also Bitwarden only supports them on desktop as they are currently working on mobile support. But this will change and as they follow a standard it will be no problem to log into apps with passkeys as the support widens.
Not really, right now as the password resets all undermine passkeys for many sites. One day if/when passwords get replaced then there will be a need, but that is a long way off probably. A good random password along with any 2FA is really good enough for most cases, and Bitwarden already does that very well along with even random e-mail addresses.
It’s ssh keys, basically.
Every service will have a keypair generated, managing the client keys is what all the passkey managers are doing.
Passkeys are great in that they are cryptographically secure, no guessed password issues. But now the client has to manage the keys. If you have a good workflow with your password manager, then passkeys are a strict improvement. If your workflow isn’t great, then don’t worry a out it, the benefit over strong passwords isn’t huge yet.
I don’t like passkeys yet because they’re implemented poorly on most platforms, IMHO, because they replace two factors with one. Some don’t let you also turn on two factor auth at all which is dumb, but the ones that do then often only have options that use your device as a factor either through text or email. So if the passkey is your phone and you add text messages as the 2 factor option, that’s still your phone. Or if your passkey is your laptop and you’re logged into your email on the laptop, it’s just one.
Passkeys are 2FA
Could either you or @[email protected] explain this for me? If all that’s required to log in using a passkey is access to a single device/provider (e.g. Proton Pass in this case) how does it replace 2FA?
For an authentication flow to qualify as two factor authentication, a user must verify at least two factors - and each must be from the following list:
- something they know, like a password
- something they have, like a phone or security key
- something they are - fingerprints, facial recognition (like FaceID), iris scans, etc…
Passkeys require you to verify a password or authenticate with biometrics. That’s one factor. The second factor is having the passkey itself, as well as the device it’s on.
If you login to your password manager on your phone and use your fingerprint to auth, that’s two factors right there.
But authentication to access the passkey is on a remote device. So the server doesn’t have any information about if or how authentication was performed for the person to access the key. If they use a 4 digit pin or, worse, the 4 point pattern unlock, it’s easy enough to brute force on most devices.
This is also why using a password manager is not two factor authentication. It is one factor on your device and one factor on the server. But no one monitors the security logs on the device to detect brute force attacks and invalidate keys. Most don’t even wipe the device if the pin is being brute forced.
None of what you’re saying has anything to do with whether an authentication flow is effectively implementing two-factor authentication.
The server doesn’t need to know details about which two factors you used. If you auth with a passkey and it knows that passkeys themselves require an additional factor to be used, then it knows that you’re using 2FA.
If they use a 4 digit pin or, worse, the 4 point pattern unlock, it’s easy enough to brute force on most devices.
This is true, but that doesn’t mean it doesn’t qualify as an authentication factor. Nobody should use a 4-6 digit PIN for their phone, but this is a matter of individual security preferences and risk tolerance. In a corporate setting, the corporation can set the minimum standard here in accordance with their own risk tolerance.
My password could be “password123” and it would still be one factor.
I’m not saying it doesn’t count as authentication, it just doesn’t count as authentication to the security of the server directly. That’s the device’s security and configured by the user, not the server. And user devices are very prone to exploits to the point that many law enforcement agencies don’t even bother asking for a password anymore to access a device.
So, let’s move to a physical model as an example. Let’s say you have a door. It has a very simple door handle lock. You keep your key inside a hotel safe. Sure it might be difficult to get the key if they had to enter the hotel room, cut open the safe in place, and get the key while they’re standing in front of the secure door, exposed. But that’s dumb. They could just as easily grab the safe out of the room and open it later where there’s room for proper equipment, use a known exploit for the particular safe, or use other exploits all out of view of the door/server and at any time until the user realizes you know how to open their safe, because the door/server will never find out. Once that safe is open, you have not just the key to the door, but the key to all locks the user uses since now we only have “something you have” factors and the user uses only one device. Just like when we only had “something you know” factors and the user uses the same password everywhere.
So what does the passkey help with? It makes the lock and thus the key itself more complex. This makes it so that brute force attacks against the server are more difficult. But it doesn’t solve anything that existing TOTP over text messages didn’t solve, other than some complexity, and it eliminated the password (something you know) factor at the server. Something a lot of companies are already doing and we already know from experience is a bad practice. It has changed the hacking target to the device rather than the person. But still just one target, you don’t need both. Sure it’s better than a really bad password that’s reused everywhere. But it’s not better than a really good password unique to a site that’s only stored in a password manager on the user’s device that requires a separate master password to access (outside of MitM attacks that TOTP mitigates).
Now, what if we have a door with two locks, one that requires a code, and one that requires you to have access to a device. Now in order to attack the door, you need two factors right at the time you’re standing at the door. Also, there’s probably a camera at the door and someone paid to check it periodically when someone tries too many times, which isn’t the case in the user’s safe/device. So even if you get the key from the user, you still need to brute force the second lock efficiently or you need to implement a second exploit to get the second factor ahead of time. This is the idea of two factors at the server and the current state of things before passkeys.
Getting physical access to users’ devices is more difficult than compromising their passwords, so in that sense, transitioning that one factor is a net improvement in terms of reducing the number of compromises for a given service.
Except for e2ee accounts, which I suspect Passkeys don’t support in the first place (at least, not without caching the password on your device), law enforcement can access your account’s data without ever needing your password. If you’re concerned about law enforcement breaking into your device and you’re not using a unique 16+ character passcode with it set to wipe the device after a certain number of attempts, that’s on you.
I’m not sure about the state of affairs on Android, but the most popular and powerful tool used by law enforcement to extract data from iOS devices only recently gained support for iOS 17 and it doesn’t have the ability to bypass passwords on a device that isn’t accepting FaceID; it just has the ability to brute force them. A password with sufficient entropy mitigates this attack. (It’s unclear if it’s able to bypass auth when FaceID is enabled, but I could see it going either way.)
You said a couple of things that I specifically want to address:
But it doesn’t solve anything that existing TOTP over text messages didn’t solve, other than some complexity, and it eliminated the password (something you know) factor at the server.
and
outside of MitM attacks that TOTP mitigates
Text-message based TOTP - or SMA 2FA - is incredibly vulnerable. In many cases, it can be compromised without the user even realizing. A user with a 4 digit PIN (even if that PIN is 1234) and a Passkey on their device is much less vulnerable than a user using SMS 2FA with a password used across multiple services.
If a user cares deeply about security, they likely already have a set of security keys (like the YubiKey 5C) that support U2F / WebAuthn, and they’ll add passkeys for their most sensitive services to those devices, protected by unique, high entropy PINs. This approach is more secure than using an equally high entropy password and U2F / WebAuthn if the latter isn’t secured with a PIN, since these devices are extremely secure and wipe their contents after 8 failed PIN attempts, but the password is transmitted to the server, which receives it in plaintext and stores it hashed, generally outside of a secure enclave, making the password vulnerable, e.g., if grabbed from server memory, or to a brute force attack on the hash if the server (which could be undetected and only involve read access to the db server), meaning a simple theft of the security key would be all that was needed to compromise the account (vs needing the PIN that is never transmitted anywhere).
And app-based TOTP doesn’t mitigate MITM at all. The only thing it does is add a timing component requirement, which current MITM phishing attacks have incorporated. To mitigate such an attack you need Passkeys, Webauthn, or U2F as an authentication factor. To bypass this the attackers need to compromise the service itself or a certificate authority, which is a much taller task.
The other thing is that we know most users reuse passwords and we know that sites will be compromised, so:
- best case scenario, salted password hashes will be leaked
- likely scenario, password hashes will be leaked,
- and worst case scenario, plain text passwords will be leaked
and as a result, that user’s credentials for a different site will be exposed. For those users, Passkeys are a vast improvement over 1FA, because that vulnerability doesn’t exist.
Another factor is the increased visibility of Passkeys is resulting in more sites supporting them - U2F / Webauthn didn’t have great adoption. And getting these into the hands of more users, without requiring them to buy dedicated security keys, is a huge boost.
For the vast majority of users, passkeys are an improvement in security. For the few for whom they aren’t, those users likely know that, and they still benefit from increased adoption of a MITM immune authentication method, which they can choose on a site-by-site basis. And even they can benefit from increased security by storing passkeys on a security key.
A passkey that’s generated on any given device is tied to that device, and is never sent to the server you’re authenticating to. What’s sent instead is a time based challenge/response that functions similarly to TOTP except that it’s not based on a shared secret like TOTP is. Since the Passkey is both a file, and is tied to the device you generated it on, it satisfied the something you have factor. Then in order to use a Passkey to authenticate, you need to unlock access to it using either biometrics (something you are) or a PIN (something you know).
Now storing your passkeys in a password manager does muddy the process of it a bit. The “something you have” part is no longer a device, but the key file itself, which is still arguably “something you have” but it is to a degree less secure than keeping it tied to a device. But you can think of storing passkeys in a password manager similarly to storing your TOTP in your password manager. It’s a tradeoff.
I know that with 1Password, even if I authenticate to my vault using my master password, when I go to use any particular passkey, it still requires biometrics.
Problem is that if the factor is not authenticated by the server, it doesn’t count. Not saying it’s not helpful, but it’s not part of the consideration when designing the security of the system.
The device can be attacked for an indefinite time and the server knows nothing about that. Or the device can disable that additional security either knowingly or maliciously and the server has no knowledge of that breach. So it’s still a single factor, “something you have” to the perspective of the server when considered security.
I’ve worked with healthcare data for decades and am currently a software architect, so while it’s not my specialty directly, it is something I’ve had to deal with a lot.
That’s because it’s not 2FA, strictly speaking. The second factor is whatever the device uses to verify you. So, essentially:
You go to a webpage, then go to sign up. Instead of inputting a password, you just input some ID, like a username or email. The device generates a cryptographic handshake with the webpage and your ID. You don’t (can’t, unless you can memorize a string of thousands of letters and numbers and be really good at math with prime numbers) have to remember it.
Now, when you go to login to that page again, the device just remembers and exchanges the keys with the webpage for you. That is NOT 2FA. But, you can configure your device to require another verification (most do). So, when you go to login, then the device asks you to use your fingerprint, or a remembered PIN. Or whatever that confirms that the one handling the device is indeed you before sharing encryption keys with the webpage. This is sorta 2FA, but not really because the webpage is delegating the second factor to the same device actually doing the login. Which might be compromised altogether, but that already happens with most 2FA implementations.
If you go to a second device, and wish to login, then your second device will fallback to other 2FA versions, like sending a OTP to the verified email or phone, or asking you to verify on the one device that is already logged in.
I believe passkeys are supposed to replace 2FA and passwords. If you have a passkey, you’re not supposed to need 2FA.
Does it beat Bitwarden though? Bitwardan has supported at least 2 services for me using passkeys ,one of which is google.
I might be misunderstanding this,but it doesn’t seem like proton beat anyone to anything.
Edit for info: https://bitwarden.com/passwordless-passkeys/
They’re talking about the fact that Bitwarden doesn’t support passkeys on mobile
Right,yeah,that’s true for mobile indeed.
Sad that these sort of features are paywalled.
Why shouldn’t these features require money?
It’s $10 per YEAR. This is an extremely reasonable price given the importance of the service.
Bitwarden employees need to eat too.
I’d be perfectly okay with them just charging for Bitwarden, period. Instead they pretend it’s free but charge premium for all the most effective security features, including 2FA to their own services. Effectively it creates a group of people that use Bitwarden without access to these security features but complacent enough to not seek alternatives that would offer these features at a price acceptable for them (possibly free, like KeepassXC).
Bottom line: security shouldn’t be a premium feature. It should be either available or not at all. Never as a premium within the service.
For logging in, Bitwarden supports TOTP, email, and FIDO2 WebAuthn on the free plan. It only adds Yubikey OTP and Duo support at the paid tier, and WebAuthn is superior to both of those methods. This is an improvement that they made fairly recently - back in September 2023.
The other features that the free plan lacks are:
- the 1 GB of integrated, encrypted file storage. This is a convenience that is nice to have, but not essential to a password manager.
- the integrated TOTP generator. This is a convenience that many argue is actually a security downgrade (under the “putting all your eggs in one basket” argument).
- Upgraded vault health reports - free users get username data breach reports but not weak / reused password reports. This is the main area where your criticism is valid, but as far as I know free competitors don’t offer this feature, either. I looked at KeepassXC and didn’t see this mentioned.
- Emergency access (basically a trusted contact who can access your vault under some circumstances). This isn’t essential, either, and the mechanisms they add to ensure security of it cost money to provide.
- Priority support - free users get 24/7 support by email, which should be good enough
I wasn’t aware they added WebAuthn to the free plan recently. That’s great to hear, thanks for the correction!
I disagree.
Simply adopting the use of their free service (or any password manager, sans 2FA) is an upgrade in terms of personal security. That’s moving in the right direction from memorized (and let’s be honest, that means using the same or a small list of similar passwords) passwords everywhere.
The existence of alternatives that include 2FA at no cost works against your point IMO. But that also comes at a cost - Keepass requires that you manage your own sync and backup.
It’s not paywalled. It’s not yet implemented in mobile bitwarden apps. It probably won’t be paywalled once implemented because it’s not paywalled in extension where it’s already implemented
2FA is a paid feature in Bitwarden. That’s the feature we were talking about.
Edit: fuck me for explaining myself
You’re getting downvoted because that, in fact, isn’t the feature we were talking about.
2FA and passkeys are different
The point of the post was that Proton Pass is beating Bitwarden right now to having passkeys for mobile (Bitwarden has still not released that), and Proton Pass can actually export passkeys which Bitwarden does not do, so they are improving. I would not say though they are better all round than Bitwarden. I pay for both but am still evaluating the rest of Proton Pass vs Bitwarden especially around tweaks in options. But Proton is showing some innovation and momentum, while Bitwarden is slowing a bit. For those already using Proton they will likely find Proton Pass good enough to use right now.
I started using Strongbox on iPhone & Mac for passkey support Bitwarden is still there too, esp for PC, but I may move to an all KeePass setup.
The real question is why the fuck is this guy passing for two password managers if not more, especially if he isn’t even using one?